Aside from being an implementation nightmare, I think the proposal in this RFC is strictly better than props-in-style — it gives you the same expressive power in a neater, more idiomatic way, along with the global theming ability.
- Sep 2020
-
github.com github.com
-
-
github.com github.com
-
docs.google.com docs.google.com
-
I’ve seen some version of this conversation happen more times than I can remember. And someone will always say ‘it’s because you’re too used to thinking in the old way, you just need to start thinking in hooks’.
But after seeing a lot of really bad hooks code, I’m starting to think it’s not that simple — that there’s something deeper going on.
-
-
stackoverflow.com stackoverflow.com
-
being able to compose multiple components' functionality via decoration (not creating new "combo" components or something) is more elegant, and something I wish React had.
-
-
-
Can you try to delete node_modules folder and package-lock.json file.
-
clean node_modules
-
Between each step I did rm -rf node_modules package-lock.json && npm i. Just to be sure
-
- Aug 2020
-
meta.stackexchange.com meta.stackexchange.com
-
Can't upvote this enough. It is highly irritating to see language destroyed (and we wonder why kids bastardize the language..).
Tags
- correctness
- example of: using incorrect terms
- combating widespread incorrectness/misconception by consistently doing it correctly
- hoping/trying to convince others that your view/opinion/way is right by consistently sticking to it despite many being ignorant/mistaken/unaware/holding different opinion
- even if majority makes a mistake; it doesn't make it correct
Annotators
URL
-
-
english.stackexchange.com english.stackexchange.com
-
As a web designer, I hate that "log in" creates a visual space between the words. If you line up "Log In Register" - is that three links or two? This creates a Gestalt problem, meaning you have to really fiddle with spacing to get the word groupings right, without using pipe characters.
Sure, you can try to solve that problem by using a one-word alternative for any multi-word phrase, but that's not always possible: there isn't always a single word that can be used for every possible phrase you may have.
Adjusting the letter-spacing and margin between items in your list isn't that hard and would be better in the long run since it gives you a scalable, general solution.
"Log in" is the only correct way to spell the verb, and the only way to be consistent with 1000s of other phrasal verbs that are spelled with a space in them.
We don't need nor want an exception to the general rule just for "login" just because so many people have made that mistake.
-
I don't doubt that we will soon treat the process of logging in as a figurative point of entry, meaning that log into will make full conceptual sense (cf you don't physically delve into a problem or pile into an argument, yet both are correct grammatically because they are semantically [i.e. figuratively])
Tags
- relying on luck/coincidence
- word that has a generic/figurative meaning in addition to a specific/literal meaning
- weak argument
- should not infer as a general rule
- language: figurative use of word
- solving/handling the general case
- trying to make a general rule out of something that only works for certain specific cases
Annotators
URL
-
- Jul 2020
-
www.pcworld.com www.pcworld.com
-
Oracle didn’t seem very interested in OpenOffice.org, and the community of volunteers developing it formed The Document Foundation back in 2010. They called on Oracle to participate and donate the OpenOffice.org name and brand to the community. Oracle never did, and the resulting forked office suite has been named LibreOffice since then.
-
-
edpb.europa.eu edpb.europa.eu
-
For example, as the GDPR requires that a controller must be able to demonstrate that valid consentwas obtained, all presumed consents of which no references are kept willautomatically be below theconsent standard of the GDPR and will need to be renewed. Likewise as the GDPR requires a“statement or a clear affirmative action”, all presumed consents that were based on a more impliedform of action by the data subject (e.g.a pre-ticked opt-in box) will also not be apt to the GDPRstandard of consent.
-
-
www.iubenda.com www.iubenda.com
-
The cookie banner will be displayed any time a user visits your site for the first time or when you have decided to add a new vendor to your list of vendors (since it’s a new disclosure and potentially a consent request for that vendor may be required).
-
-
-
First, let's make it clear that NODE_ENV has no explicit relationship to RAILS_ENV. Setting one of the ENV variables will have no effect on the other.
-
-
discuss.rubyonrails.org discuss.rubyonrails.org
-
And you see the problem, concerns are so simple that they do not deserve a full guide. Concerns are mixins, if you are a Ruby programmer, you already know what a mixin is and their use case to modularize APIs.
-
- Jun 2020
-
stackoverflow.com stackoverflow.com
-
What would be nice is if JavaScript had a built-in way to do what I can do in Ruby with:
> I18n.interpolate('Hi, %{name}', name: 'Fred') => "Hi, Fred"But to be fair, I18n comes from i18n library, so JS could just as easily (and I'm sure does) have a library that does the same thing.
Update: Actually, you can do this in plain Ruby (so why do we even need
I18n.interpolate?):main > "Hi, %{name}" % {name: 'Fred'} => "Hi, Fred"main > ? String#% From: string.c (C Method): Owner: String Visibility: public Signature: %(arg1) Number of lines: 9 Format---Uses str as a format specification, and returns the result of applying it to arg. If the format specification contains more than one substitution, then arg must be an Array or Hash containing the values to be substituted. See Kernel::sprintf for details of the format string. "%05d" % 123 #=> "00123" "%-5s: %016x" % [ "ID", self.object_id ] #=> "ID : 00002b054ec93168" "foo = %{foo}" % { :foo => 'bar' } #=> "foo = bar"I guess that built-in version is fine for simple cases. You only need to use
I18n.translateif you need its more advanced features likeI18n.config.missing_interpolation_argument_handler.
-
-
stackoverflow.com stackoverflow.com
-
gist.github.com gist.github.com
-
edgeguides.rubyonrails.org edgeguides.rubyonrails.org
-
If you've found a problem in Ruby on Rails which is not a security risk, do a search on GitHub under Issues in case it has already been reported. If you are unable to find any open GitHub issues addressing the problem you found, your next step will be to open a new one.
-
-
github.com github.com
-
It's funny that in such a complex gem like this, there's only one open issue, exactly about what I came here to post.
-
-
discuss.rubyonrails.org discuss.rubyonrails.org
-
discuss.rubyonrails.org discuss.rubyonrails.org
-
rails.lighthouseapp.com rails.lighthouseapp.com
-
I ran in to what I thought was this issue, but I was using fragment caching. Since the partial was not executed again, the content_for was not called. content_for could be written differently to handle this.
-
-
gist.github.com gist.github.com
-
Supports nested 'cache do' blocks and some fixes
-
-
rails.lighthouseapp.com rails.lighthouseapp.com
-
stackoverflow.com stackoverflow.com
-
signal.org signal.org
-
It is as though the Big Bad Wolf, after years of unsuccessfully trying to blow the brick house down, has instead introduced a legal framework that allows him to hold the three little pigs criminally responsible for being delicious and destroy the house anyway. When he is asked about this behavior, the Big Bad Wolf can credibly claim that nothing in the bill mentions “huffing” or “puffing” or “the application of forceful breath to a brick-based domicile” at all, but the end goal is still pretty clear to any outside observer.
-
For a political body that devotes a lot of attention to national security, the implicit threat of revoking Section 230 protection from organizations that implement end-to-end encryption is both troubling and confusing. Signal is recommended by the United States military. It is routinely used by senators and their staff. American allies in the EU Commission are Signal users too. End-to-end encryption is fundamental to the safety, security, and privacy of conversations worldwide.
-
At a time when more people than ever are benefiting from these protections, the EARN IT bill proposed by the Senate Judiciary Committee threatens to put them at risk.
-
-
www.forbes.com www.forbes.com
-
EFF describes this as “a major threat,” warning that “the privacy and security of all users will suffer if U.S. law enforcement achieves its dream of breaking encryption.”
-
-
www.forbes.com www.forbes.com
-
Despite its opposition, EARN-IT is the clearest threat yet to end-to-end encryption, given this clever twist in pushing the onus onto the platforms to avoid transmitting illegal content, rather than mandating a lawful interception approach.
-
Putting that risk more simply, the EARN-IT bill is cleverly leaving it to the tech platforms to keep themselves safe—there would be little option other than some form of access to encrypted content, even though it would not be specified in law. Sophos describes this as “the backdoor virus that law enforcement agencies have been trying to inflict on encryption for years.”
-
On the encryption front, HRW echoes others that have argued vehemently against the proposals—that weakened encryption will “endanger all people who rely on encryption for safety and security—once one government enjoys special access, so too will rights-abusing governments and criminal hackers.” Universal access to encryption “enables everyone, from children attending school online to journalists and whistleblowers, to exercise their rights without fear of retribution.”
-
the encryption debate continues to rage in the U.S., with proposed new legislation representing the clearest threat yet to the security underpinning WhatsApp and iMessage, as well as Signal, Telegram and Wickr
-
-
dev.mysql.com dev.mysql.com
-
Deadlocks are a classic problem in transactional databases, but they are not dangerous unless they are so frequent that you cannot run certain transactions at all. Normally, you must write your applications so that they are always prepared to re-issue a transaction if it gets rolled back because of a deadlock.
-
- May 2020
-
kellysutton.com kellysutton.com
-
“Make it work” means shipping something that doesn’t break. The code might be ugly and difficult to understand, but we’re delivering value to the customer and we have tests that give us confidence. Without tests, it’s hard to answer “Does this work?”
-
-
www.digital-democracy.org www.digital-democracy.org
-
By putting our data in the corporate cloud, we are that kid. We are giving corporations and governments a way to see where we are looking towards, and they can predict our future and decide whether and how to intervene or subvert.
-
From a game theoretic standpoint, we’ve already lost. Too many of our civil society adversaries have too much of our data, and we have so little of theirs.
-
-
www.collinsdictionary.com www.collinsdictionary.com
-
This corpus became the largest collection of English language data in the world
-
-
www.merriam-webster.com www.merriam-webster.com
-
to remove the force or effectiveness of
-
-
webapps.stackexchange.com webapps.stackexchange.com
-
I am looking for indirect access via some sort of settings or confirmation, or proof that it is impossible.
-
-
gist.github.com gist.github.com
-
iandunn.name iandunn.name
-
Unfortunately, the WordPress.org plugin repository doesn’t provide a way to maintain your plugin with Git.
-
-
teleogistic.net teleogistic.net
-
Some months ago, I wrote about using Git and Github with the wordpress.org plugin repository.
-
-
-
-
I want my Page Translator extension to be made irrelevant by Firefox having built-in language translation, like Google Chrome and Microsoft Edge. It is a critical feature used by millions of people daily. It bridged a feature gap. Mozilla killing this add-on without replacing it hurts users.
-
-
github.com github.com
-
I would love for Mozilla to make this extension irrelevant by providing the functionality natively. Language translation is a standard and yet highly differentiating feature in Chrome and Edge.
-
I wish Mozilla would recognize the importance of built-in translation that Google Chrome and Microsoft Edge have.
-
- Apr 2020
-
iapp.org iapp.org
-
the cost of reading consent formats or privacy notices is still too high.
-
Third, the focus should be centered on improving transparency rather than requesting systematic consents. Lack of transparency and clarity doesn’t allow informed and unambiguous consent (in particular, where privacy policies are lengthy, complex, vague and difficult to navigate). This ambiguity creates a risk of invalidating the consent.
systematic consents
-
the authority found that each digital platform’s privacy policies, which include the consent format, were between 2,500 and 4,500 words and would take an average reader between 10 and 20 minutes to read.
-
-
www.troyhunt.com www.troyhunt.com
-
many organisations block torrents (for obvious reasons) and I know, for example, that either of these options would have posed insurmountable hurdles at my previous employment
-
Actually, I probably would have ended up just paying for it myself due to the procurement challenges of even a single-digit dollar amount, but let's not get me started on that
-
Amazon has got a neat Requestor Pays Feature but as soon as there's a cost - any cost - there's a barrier to entry.
-
-
stackoverflow.com stackoverflow.com
-
[link](url){:target="_blank"} Works for jekyll or more specifically kramdown, which is a superset of markdown, as part of Jekyll's (default) configuration. But not for plain markdown. ^_^
-
-
stackoverflow.com stackoverflow.com
-
For ghost markdown use: [Google](https://google.com" target="_blank) Found it here: https://cmatskas.com/open-external-links-in-a-new-window-ghost/
-
-
tenderlovemaking.com tenderlovemaking.com
-
Now, do I care which one you use? No. As long as you test your code, I am happy. A professional developer should be able to work in either one of these because they essentially do the same thing: test your code.
-
-
gavinmiller.io gavinmiller.io
-
You see entropy is information leaking. When it comes to passwords (and secure systems in general) you want to leak as little information as possible. Otherwise an attacker has information they can use to their advantage.
-
-
-
since mobile Chrome still doesn't support extensions (Google plz)
-
-
www.csoonline.com www.csoonline.com
-
Download the billions of breached passwords and blacklist them all. Attackers have a copy; so should you.
-
-
blog.1password.com blog.1password.com
-
This isn’t the first time Kerckhoffs’ Principle has come up. I specifically discussed it when talking about creating good, strong Master Passwords, when I said that we should use a system for coming up with Master Passwords that doesn’t lose its strength if the attacker knows the system that we used
-
Kerckhoffs’ Principle states that you should assume that your adversary knows as much about the system you use as you do. This is why – despite what I may have said on April Fools Day last year – security experts are skeptical of security systems that hide the details of how they operate. They are particularly skeptical of systems that derive their security from keeping the details of how they work secret. I could go on at great length about why openness about the system improves security. Indeed, my first draft of this article did go on at great length.
-
-
en.wikipedia.org en.wikipedia.org
-
"the enemy knows the system"
-
"one ought to design systems under the assumption that the enemy will immediately gain full familiarity with them"
-
-
www.techrepublic.com www.techrepublic.com
-
there's no reasonable way to communicate effectively with the less technically minded without acquiescing to the nontechnical misuse of the term "hacker"
-
The more easily relabeled of the two uses of the term "hacker" is the malicious security cracker: it is not only the more recent phenomenon to acquire that label, but also the one whose meaning is most easily evoked by an alternative term. This is why, when you read an article of mine that talks about malicious security crackers, I use the term "malicious security cracker"
Tags
- communicating with less technical people
- alternative to mainstream way
- hoping/trying to convince others that your view/opinion/way is right by consistently sticking to it despite many being ignorant/mistaken/unaware/holding different opinion
- "hacker" vs. "cracker"
- language: misuse of word
- language
- communication
- acquiescing/giving in
- popular misconceptions
Annotators
URL
-
-
web.archive.org web.archive.org
-
support.1password.com support.1password.com
-
1Password wasn’t built in a vacuum. It was developed on top of open standards that anyone with the right skills can investigate, implement, and improve. Open tools are trusted, proven, and constantly getting better. Here’s how 1Password respects the principles behind the open tools on which it relies:
I found it ironic that this proprietary software that I have avoided using because it is proprietary software is touting the importance of open tools.
-
-
www.kickstarter.com www.kickstarter.com
-
We wondered - do voters carefully consider the political issues and then objectively study each candidate’s platform, or do they mainly go with from-the-gut “tribal” feelings?
-
-
accessmedicine.mhmedical.com accessmedicine.mhmedical.com
-
The final stages of this sequence are caused by blood accumulation that forces the temporal lobe medially, with resultant compression of the third cranial nerve and eventually the brain stem.
-
-
wordpress.org wordpress.org
-
Automattic uses WordPress to power WordPress.com, and it contributes back code and time to the WordPress project. It is a symbiotic relationship. It isn’t accurate to say that WordPress is Automattic’s product, or that WordPress came from Automattic. Indeed, the opposite is true — Automattic came from WordPress, and Automattic (through WordPress.com) exists as part of the vast WordPress community and ecosystem.
That's probably a common misconception. I'm glad they clarified that because I might have assumed that as well:
It isn’t accurate to say that WordPress is Automattic’s product, or that WordPress came from Automattic. Indeed, the opposite is true — Automattic came from WordPress, and Automattic (through WordPress.com) exists as part of the vast WordPress community and ecosystem.
-
- Mar 2020
-
techcrunch.com techcrunch.com
-
Because humans hate being bored or confused and there are countless ways to make decisions look off-puttingly boring or complex — be it presenting reams of impenetrable legalese in tiny greyscale lettering so no-one will bother reading
-
-
guides.rubyonrails.org guides.rubyonrails.org
-
For several reasons the Simple backend shipped with Active Support only does the "simplest thing that could possibly work" for Ruby on Rails3 ... which means that it is only guaranteed to work for English and, as a side effect, languages that are very similar to English. Also, the simple backend is only capable of reading translations but cannot dynamically store them to any format.That does not mean you're stuck with these limitations, though. The Ruby I18n gem makes it very easy to exchange the Simple backend implementation with something else that fits better for your needs, by passing a backend instance to the I18n.backend= setter.
-
-
www.osano.com www.osano.com
-
"I have read and agree to the terms and conditions” may well be the most common lie in the history of civilization. How many times do you scroll and click accept without a second thought? You’re not alone. Not only they go unread, but they also include a self-updating clause requiring you to go back and review those documents for changes. You’re agreeing to any changes, and their consequences, indefinitely.
-
-
www.vox.com www.vox.com
-
And, frankly, we’re abetting this behavior. Most users just click or tap “okay” to clear the pop-up and get where they’re going. They rarely opt to learn more about what they’re agreeing to. Research shows that the vast majority of internet users don’t read terms of service or privacy policies — so they’re probably not reading cookie policies, either. They’re many pages long, and they’re not written in language that’s simple enough for the average person to understand.
-
But in the end, they’re not doing much: Most of us just tediously click “yes” and move on.
-
The site invites you to read its “cookie policy,” (which, let’s be honest, you’re not going to do), and it may tell you the tracking is to “enhance” your experience — even though it feels like it’s doing the opposite.
-
-
www.osano.com www.osano.com
-
Mission Driven Culture
-
- Jan 2020
-
www.budibase.com www.budibase.com
-
Your idea should stem from solving someone’s problem. Ideally, your own problem. It’s important that you choose an idea which interests you. Interest is key to fuelling motivation which is crucial when making a web app. It takes effort building web apps and it’s important you have fun during the process.
-
- Dec 2019
-
askubuntu.com askubuntu.com
-
FYI for later travellers, it looks like the comment in question by @FreeSoftwareServer has been removed.
-
-
unixwiz.net unixwiz.net
-
I would rather you vote against my position because you had an opposing view than vote with my position because you flipped a coin.
-
-
opensource.com opensource.com
-
No backup regimen would be complete without testing. You should regularly test recovery of random files or entire directory structures to ensure not only that the backups are working, but that the data in the backups can be recovered for use after a disaster. I have seen too many instances where a backup could not be restored for one reason or another and valuable data was lost because the lack of testing prevented discovery of the problem.
-
-
github.com github.com
-
Note You are viewing the README for the development version of Capybara. If you are using the current release version you can find the README at
-
-
codefund.io codefund.io
-
We do not track, profile, or sell information. We do not use cookies. We only show ads that are relevant and meaningful to the users.
-
- Nov 2019
-
-
I'm considering this, although I'm still leaning towards not including it and I'd love to just get rid of first if it wouldn't break so many peoples tests. Newcomers to Capybara don't understand (or aren't willing to learn) the issues that all/first (and last if added) have and massively overuse them. Yes the fact that all and first now wait by default will prevent some of the new user issues/confusion, but it won't fix the non-reloadability issue.
-
-
github.com github.com
-
I often wish for this. I don't understand why this hasn't been added.
Ugly workaround for now:
# Note, even though we don't need or use arguments passed to this selector, you *must* pass in an # argument to prevent it from matching the :id selector and giving a "Unable to find id :parent (Capybara::ElementNotFound)" error. # Example: el.first(:parent, 1) # You may also need match: first if el matches multiple elements to avoid Capybara::Ambiguous Capybara.add_selector(:parent) do xpath { ".//.." } end
-
-
www.gao.gov www.gao.gov
-
vulnerabilities in industrial control system devices before patches can be applied.
Unsure about this. There are various threat detection methods... unless there are APT actors using things like zero days. ... Or I guess really anyone acquiring zero-days on darknet?
-
- Oct 2019
-
-
For the uninitiated, Granny Smith was Maria Ann Smith, a resident of the area who in 1868 "accidentally" grew the first batch of green apples that now bear her name.
Yes, good thinking. Throw in a truthful fact or two. Impressive!
-
-
www.geek.com www.geek.com
-
Their hope by announcing so loudly what they have accomplished, is that others in the Android modder/hacker scene will step up and help them turn this root exploit into something useful for users by deploying features that are not currently available through the Google controlled Chromecast experience.
-
- Sep 2019
-
atomicobject.com atomicobject.com
Tags
Annotators
URL
-
-
atomicobject.com atomicobject.com
-
MASTERY, AUTONOMY, PURPOSE
-
- Aug 2019
-
answers.microsoft.com answers.microsoft.com
- Jul 2019
-
ohiostate.pressbooks.pub ohiostate.pressbooks.pub
-
We will study how a Disc Jockey’s (DJ’s) endorsement of recording on radio, in the 1950s, could boost sales into the millions.

-
- Apr 2019
-
hypothes.is hypothes.is
-
The music we listen to highly impacts our decision making, especially as adolescents. Adolescents are extremely impressionable, and the music they listen to has a great impact on how they decide to live their day to day lives. Popular musicians are seen as role models by the people who idolize them, and adolescents may try to represents the songs in which they favor through their actions every day.
Recent studies have found that adolescents who listen to music that supports substance abuse and violence have a greater chance to act upon what they listen to. What young adults and teenagers listen to through music and popular media will affect their decision making process. Specifically with substance abuse, and there is a direct uptake in use of illegal substances by adolescents who listen to music that promotes such activities. This can cause a whole societal problem considering most of todays popular music among adolescents touches upon substance abuse and violence. Adolescents are extremely impressionable and the music they listen can shape how a person tries to act, or represent themselves.
-
- Feb 2019
-
human.libretexts.org human.libretexts.org
-
this
I thought the point that the father made about why he put his son in the art of boxing to teach him about being a man at 7 years old. I mean i agree with the lady about him getting hurt in boxing at the age of 7 years old.
-
-
static1.squarespace.com static1.squarespace.com
-
ince sounds have no natural connection with our ideas,
-
- Jan 2019
-
static1.squarespace.com static1.squarespace.com
-
new subjects of knowledge
Melvil Dewey: "Guess I'll forget the base 10 number system and switch to hexadecimal."
For real, she's proposing developing knowledge that is outside of Dewey's ordering system. It's like 150 years old; it's about time!
-
- Sep 2018
-
cnx.org cnx.org
-
I dont believe some of this, blacks never had a voice during . That time if they were to speak up during that time they would often get punished. Blacks had no say in there freedom, slavery wasn't abolished to help slaves, Abraham Lincoln didn't do it out of the kindness out of his heart.
Tags
- https://hypothes.is/groups/q2jXEin4/f18-51-hybrid)
- Although some abolitionists were wealthy white men, most were ordinary people, including men and women of both races. White women and blacks were able to actively assist in the campaign to end slavery despite the fact that, with few exceptions, they were unable to vote. Similarly, the right to vote once belonged solely to white men until the Fifteenth Amendment gave the vote to African American men.
Annotators
URL
-
- Mar 2018
-
www.arrantpedantry.com www.arrantpedantry.com
-
That, on the other hand, is a system all by itself, and it’s rather restricted in its range. It only forms restrictive relative clauses, and then only in a narrow range of syntactic constructions. It can’t follow a preposition (the book of which I spoke rather than *the book of that I spoke) or the demonstrative that (they want that which they can’t have rather than *they want that that they can’t have), and it usually doesn’t occur after coordinating conjunctions. But it doesn’t make the same personhood distinction that who and which do, and it functions as a relative adverb sometimes. In short, the distribution of that is a subset of the distribution of the wh words. They are simply two different ways to make relative clauses, one of which is more constrained.
One of the best explanations of why relative "that" isn't a pronoun.
-
- Feb 2018
-
hypothes.is hypothes.is
-
My daughter will be brought up to understand her true value. That’s a promise. As for all the little girls to be born around the world, the creation of these ads is an effort to show how imagination can change the conversation around their lives.
-
-
archive.org archive.org
-
or
"I have, in the following little volume, collected a few of these, the Love-Songs of a single province merely, which I either took down in each county of Connacht from the lips of the Irish-speaking peasantry - a class which is disappearing with most alarming rapidity - or extracted from MSS, in my own possession, or from some lent to me, made by different scribes during this century, or which I came upon while examining the piles of modern manuscript Gaelic literature that have found their last resting-place on the shelves of the Royal Irish Academy." (iv)
The way Hyde makes reference to sources is casual and non-specific. It would be difficult for a reader to access his sources. Because we have such little insight, it is important to be alert to potential biases in the collecting and editing process.
If we can identify consistencies among the anthologized songs in terms of their depiction of love and lovers, and/or among songs which are excluded from the anthology, we will have reason to regard the very partial disclosure of sources with suspicion.
As I have already noted, part of Hyde’s project is to bring the reader into contact with language which has an ‘unbounded’ power to excite the Irish Muse. Perhaps part of the way he contrives this encounter is to control the kind of subject matter that will appear to the reader as that which occurs most naturally in the Irish language.
-
- Jan 2018
-
app.safetyculture.io app.safetyculture.io
-
There are no audits matching your search
There are no audits matching your search for Dispensary There are no audits matching your search for Cannabis There are no audits matching your search for Marijuana There are no audits matching your search for nutraceutical
-
- Dec 2017
-
www.wired.com www.wired.com
-
In a classic case of “turning a bad thing into a good thing,” however, Xiaomi used its near-fatal stumble to fashion a radical new business model.
-
- Feb 2017
-
static1.squarespace.com static1.squarespace.com
-
an eter-nally repeated dream would certainly be felt and judged to be reality.
-
-
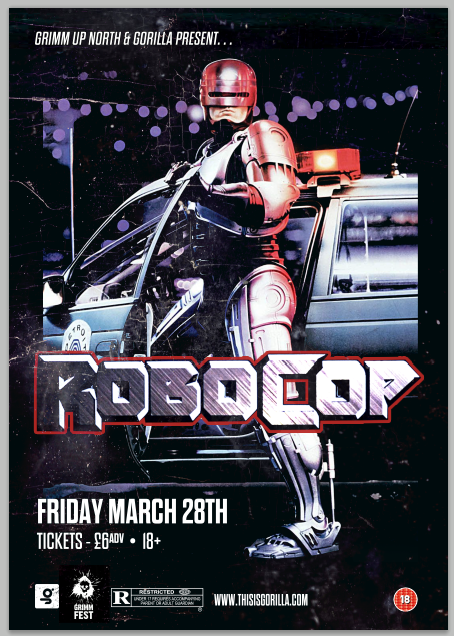
thefunambulist.net thefunambulist.net
-
Rather than acting through a model of exclusion or opposition, ‘normalisation’ assimilates the ‘abnormal’ as part of the ‘normal’ state and its proper function, turning the body into an object of strict control and under constant surveillance.
These same anxieties are the focus of so many post-human science fiction films (particularly those from the 80's) where an abnormal human body is normalized. The language of this passage especially reminded me of Robocop where the protagonist effectively loses control over his body and is constantly surveilled by his corporate creators.
-
- Jan 2017
-
-
highlighted
And here we go down the rabbit hole....
Tags
Annotators
URL
-
- Dec 2016
-
sites.google.com sites.google.com
-
You gotta go for what you knowMake everybody see, in order to fight the powers that beLemme hear you sayFight the Power
This shows how Public enemy started a physical movement among the people. Many took to the streets to participate in non-violent protests for the cause. Many were forced to hear what they had to say and there was a push for change. Public Enemy never wanted the protest to be violent, they just wanted change.
-
- Apr 2016
-
dl.dropboxusercontent.com dl.dropboxusercontent.com
-
isn’t that (3)
Demonstrativt pronomen: peger tilbage til noget fra en tidligere sætning
-
they knew that (4) they could sit their child in front of a Disney video
Konjunktion: forbinder ledsætningen "they knew" med den definerende relativsætningen "they could sit their child in front of a Disney video"
-
three main issues that (5)
Relativt pronomen: henviser til "three main issues"
-
advertisement that (1) promised us
Relativt pronomen: henviser til "a stunning Superbowl advertisement"
-
that (2), “1984 won’t be like 1984”
Konjunktion: forbinder ledsætningen "that promised us" med hovedsætningen "1984 won’t be like 1984"
-
- Nov 2015
-
www.mmcr.us www.mmcr.us
-
distributing pamphlets that urged an overthrow of the government
The pamphlets were urging the resistance of the draft, but the book did not state that the attempt was to overthrow the government. Only to express his political ideals.
-
- Oct 2015
-
hypothes.is hypothes.is
-
The articles obtained to review Trick Your Brain into Thrift by Paying with Cash by Crack Articles is a theory that can be held at both ends. The articles provided have several brushed details of numerous researches that have been done that links the psychological human being into using credits card. Vis versa there is not much details on how to make, trick, or psychologically change one’s mind into purchasing with cash. The psychological research lead to how one views cash and a credit card or how the individual’s emotions are effected by their economic stand point when making purchases. The types of sources influence by the credit card companies to encouraging the public into using their credit card are endless, but the top mechanism used today is earning money back while spending. A real soother to human ear, when one does not like to see cash disappear from their wallet. Acknowledging, the basis of the title that Cracked Article uses is clearly avoiding using cash. The title shouldn’t be Trick Your Brain into Thrift by Paying with Cash, but the Tricks Your Brain Uses to Have You Pay with Credit Cards or When Not to Shop to Be Thrift.
-
-
hypothes.is hypothes.is
-
Show
The NSA is still spying on you—so why did Americans stop caring?
Tags
Annotators
URL
-
- Mar 2015
-
www.scrumguides.org www.scrumguides.org
-
an objective set for the Sprint that can be met through the implementation of Product Backlog. It provides guidance to the Development Team on why it is building the Increment. It is created during the Sprint Planning meeting. The Sprint Goal gives the Development Team some flexibility regarding the functionality implemented within the Sprint. The selected Product Backlog items deliver one coherent function, which can be the Sprint Goal. The Sprint Goal can be any other coherence that causes the Development Team to work together rather than on separate initiatives.
an objective set for the Sprint that can be met through the implementation of Product Backlog. It provides guidance to the Development Team on why it is building the Increment. It is created during the Sprint Planning meeting. The Sprint Goal gives the Development Team some flexibility regarding the functionality implemented within the Sprint. The selected Product Backlog items deliver one coherent function, which can be the Sprint Goal. The Sprint Goal can be any other coherence that causes the Development Team to work together rather than on separate initiatives.
Tags
- mağaza
- an objective set for the Sprint that can be met through the implementation of Product Backlog. It provides guidance to the Development Team on why it is building the Increment. It is created during the Sprint Planning meeting. The Sprint Goal gives the Development Team some flexibility regarding the functionality implemented within the Sprint. The selected Product Backlog items deliver one coherent function, which can be the Sprint Goal. The Sprint Goal can be any other coherence that causes the Development Team to work together rather than on separate initiatives.
- hepsini sor
Annotators
URL
-